Applies To
- Zenoss Resource Manager 5.x
Summary
This KB is designed to be a quick primer on datasource creation. It uses the case of monitoring an SSL certificate as the example.
Procedure
The following procedure describes how to create a new data source:
- From within the RM GUI, make a local template.
Click the gear icon on the bottom left to launch the new template dialog. - Name the new template, any name you like.
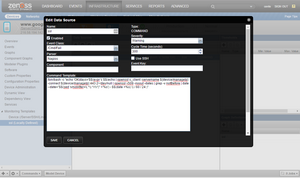
- Create a new datasource.
Click the plus (+) icon at the top and select command from the list. In this example it is named ssl. The Edit Data Source dialog displays. - Enter the following into the Command Template field:
/bin/bash -c "echo 'OK|days='$$(expr ( $$(echo | openssl s_client -servername ${device/manageIp} -connect ${device/manageIp}:443 2>/dev/null | openssl x509 -noout -dates | grep -v notBefore | date --date="$$(sed 's/notAfter=(.)./\1/')" +'%s') - $$(date +%s) ) / 60 / 24 )" - Complete any fields that you require.
- Click SAVE to save and close the dialog.
Command Notes
Dollar signs ($) in Commands
Commands that would normally have a single dollar sign ($), such as a nested argument like the first $(expr) require two dollar signs, $$. This is because the dollar sign is used in the "TALES" engine. For more information about TALES, consult the Appendix of the Administration Guide.
An actual TALES variable, ${device/manageIp}, is shown in the example code (above) with a single dollar sign that inserts the monitored device's IP. Anything that is not a TALES variable that contains a dollar sign must be escaped so it does not attempt to interpret the section after.
Use of /bin/bash Before Command
The command is prefixed with /bin/bash to initialize paths and other system variables of the command daemon. Because a shell isn't ordinarily used, if /bin/bash is not used before the command, typing in a command such as echo creates an error because echo is defined in the path of the target operating system. After initializing with /bin/bash it is no longer necessary to use full paths for any of the commands, such as echo, expr, sed, etc.
SSH Checkbox
The use ssh checkbox toggles between running this command on the monitoring server versus running the command on the target server. In this case it is left unchecked because google.com is accessible from the monitoring server.
If it is necessary to run a command that only works on the target server (for example, verify that a specific networking path is open), the check box must be ticked to run it from the other server.
Pad the Data
In the example, the data is padded with nagios format. This is because if the entire command is put into a shell, the result is something like:
OK|days=1234567890
You cannot use a command that only provides a number such as 1234567890 because the system does not understand how to use it. This is because it is possible to have multiple datapoints coming from a single command. You must label the datapoint with the command's output so it will be matched to the name of the datapoint you create in RM. For example:
Set Cycle Time
There is no need to set the cycle time to 300 (5 minutes). Because this value is updated daily, a different value might work better, such as 86400 - the number of seconds in a day.
Use Scripts
Ideally, scripts should be used that provide data even when there is no data to provide.
For example, if SSL is not installed on the target device, the associated variables can be set to 9999.
As a second example, if you want to set a datapoint called present
- Create a new datapoint called present under the datasource within RM.
- Set it to return something like OK|days=1234567890 present=1 .
- It is possible to put logic in, for example,
"if this server is running nginx,
check for an ssl;
then populate the data accordingly".
The commands depend on your particular environment. You are free to run anything that works within the target environment and limited only by your imagination.

Comments